This post was updated in April 2024.
When most people think of cyber-attacks and data breaches, they think of a hooded hacker hammering away at the keyboard in a dark corner somewhere using complex commands to get past firewalls and steal passwords.
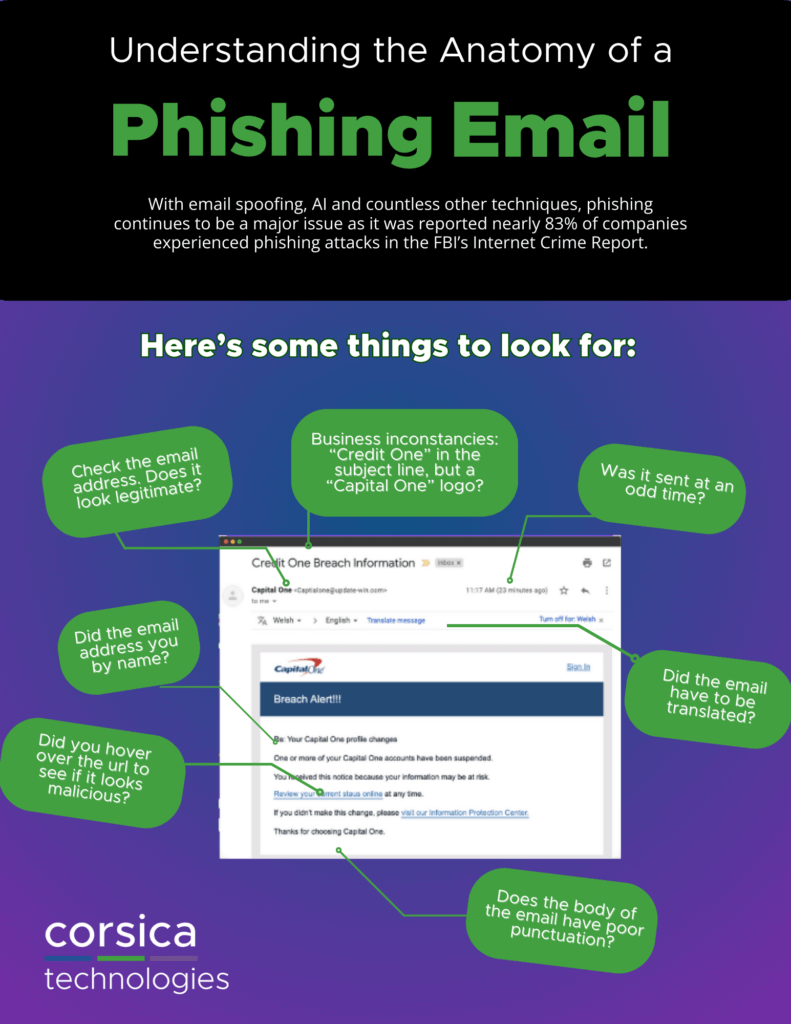
The reality is that impostor emails, or phishing emails, are the most common entry point for hackers.
And unfortunately, the perpetrators of this simple scam don’t have to know a lick of code to pull it off.
Given the success rate of phishing attacks, phishing emails will continue to be a growing problem for businesses and consumers alike. Here are just a few examples of phishing emails in use over the past year:
Download Our Guide On Spotting Phishing Email Examples
The Urgent Request
Phishing emails play to our innate psychology. By impersonating a person or organization with a high level of authority—and urging immediate action—these emails are dangerously persuasive. Whether these emails threaten loss, punishment, or added risk, researchers tell us that urging immediate action changes our focus to the singular task and, in the process, lowers our guard.
1. “Restart Your Membership”
In 2023, reported phishing attacks continued to present a significant cybersecurity challenge, reflecting the persistent threat landscape faced by individuals and organizations globally. According to the latest findings from the Anti-Phishing Working Group (APWG), the incidence of phishing attacks remained prevalent, with cybercriminals deploying increasingly sophisticated tactics to deceive users and extract sensitive information.
Additionally, reports from leading cybersecurity firms such as Symantec and McAfee corroborate the ongoing threat posed by phishing, highlighting the need for continued vigilance and robust security measures to safeguard against these malicious activities. As phishing attacks evolve in complexity and frequency, organizations and individuals must remain proactive in implementing comprehensive defense strategies to mitigate risks and protect sensitive data from compromise.
2. “Update Your Official Record”
3. “Click to Learn More”
A link embedded in an email simply saying click here to learn more, read more, take action and etc..
4. “You Missed a Delivery”
Another example of phishing is sending out a phishing email for UPS tracking slip.
Click on your tracking number and your device is immediately infected with malware.
5. “Confirm Your Account”
Embedded into your email with a button saying things like Review & Verify your account. Once you click this your computer is affected with malware within seconds.
6. “Your Account Has Been Locked”
These “Account Issues” emails take the user to dummy login pages, where the hacker conveniently — and easily — grabs login credentials, and therefore bank account, credit card numbers, and more.
7. “Suspended Account”
Download Phishing Email Examples PDF
Unexpected Refunds & Payments
It’s against our every instinct to ignore free money, and hackers exploit this with refund offers.
8. “Tax Refund”
This article here goes into great detail on how to avoid IRS scams during tax season.
9. “Refund Due to System Error”
Emails from “Major Retailers” will state things like Amazon offers a refund, click here to receive your full refund.
10. “Click to See Your Revised Salary”
Employer Fraud Phishing Example 2024 Salary Notice Human Resources Benefits
Spear-Phishing: Phishing Based on Research
Spear-phishing emails may not have the stolen logos and email templates of phishing emails, but what they do have can be even more dangerous: inside information. Spear-phishers study their victims in advance, learning names, organizational structure, and even workplace culture to try to keep the victim from raising red flags.
11. Sent “From” Recipient’s Bank
Leigh University does a great job keeping an updated collection of recent phishing examples on their site here.
12. Sent “From” Recipient’s CFO
Cyber Criminals are now sending phishing emails by using contacts within your organization in hopes that you will click on them making you vulnerable to revealing personal information. Craig McDonald provides more insight here on LinkedIn.
13. Sent “From” Recipient’s CEO requesting
All Employees W-2’s Spear Phish Email CEO Fraud.
14. Sent “From” Recipient’s CEO Fraudsters
Spoof executive leaders in email phishing attempts. Stu Sjouwerman, chief executive at security awareness training company KnowBe4 had an attempt with an email received by an employee requesting a copy of all W-2s for this year.
15. Sent “From” Recipient’s CEO
“Hi, I need you to process a wire transfer to a new vendor. Please let me know when you can get it done.” Augusta, GA Spear-Phishing Email CEO Fraud 2022; Source: Corsica Technologies
Two More Examples:
Whaling emails, or spear-phishing emails targeting high-level executives, masquerade as critical business emails from a legitimate person of authority. These emails play on our respect for these individuals and take advantage of the lack of formality that sometimes accompanies their requests.
16. Sent to VP “From” Their CEO
Phishing attacks can take many names, from CEO Fraud to Whaling and Business Email Compromise.
17. Sent to Controller “From” Their CEO (Also CCing Their Accountant)
Cyberhackers have launched CEO Fraud version 2.o sending employees emails requesting items like “Please Send our W2 Documents for all employees to… I have CC’d him here. Please send it Immediately.” Frank McKenna published an article here going more into detail about CEO Fraud 2.o.
All It Takes Is One Click
In summary, be wary of free money and urgent requests. Check unexpected emails from people in authority over the phone or in person before sharing or downloading information.
Many phishing emails only need one click to give the hacker access to your otherwise secure systems. If you’ve recently clicked on a sensitive email or want to protect your company and employees from phishing, consider phishing training and contact Corsica Technologies today to speak with an email security professional.






